Daily mail Registration Page Unvalidated Redirects and Forwards Web Security Problem
Website Description:
“The Daily Mail is a British daily middle-market tabloid newspaper owned by the Daily Mail and General Trust. First published in 1896 by Lord Northcliffe, it is the United Kingdom’s second biggest-selling daily newspaper after The Sun. Its sister paper The Mail on Sunday was launched in 1982. Scottish and Irish editions of the daily paper were launched in 1947 and 2006 respectively. The Daily Mail was Britain’s first daily newspaper aimed at the newly-literate “lower-middle class market resulting from mass education, combining a low retail price with plenty of competitions, prizes and promotional gimmicks”, and was the first British paper to sell a million copies a day. It was at the outset a newspaper for women, the first to provide features especially for them, and as of the second-half of 2013 had a 54.77% female readership, the only British newspaper whose female readers constitute more than 50% of its demographic. It had an average daily circulation of 1,708,006 copies in March 2014. Between July and December 2013 it had an average daily readership of approximately 3.951 million, of whom approximately 2.503 million were in the ABC1 demographic and 1.448 million in the C2DE demographic. Its website has more than 100 million unique visitors per month.” (Wikipedia)
One of its website’s Alexa rank is 93 on January 01 2015. The website is one of the most popular websites in the United Kingdom.
(1) Vulnerability Description:
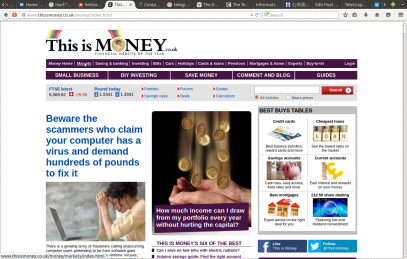
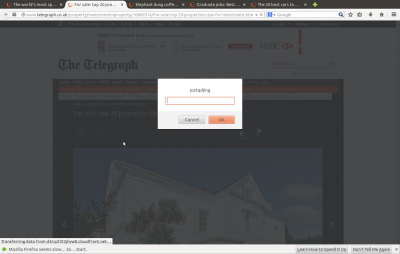
Daily online websites have a cyber security problem. Hacker can exploit it by Open Redirect (Unvalidated Redirects and Forwards) attacks. During the tests, all Daily mail websites (Daily Mail, Mail on Sunday & Metro media group) use the same mechanism. These websites include dailymail.co.uk, thisismoney.co.uk, and mailonsunday.co.uk.
Google Dork:
“Part of the Daily Mail, The Mail on Sunday & Metro Media Group”
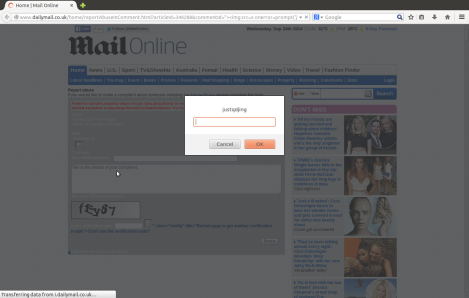
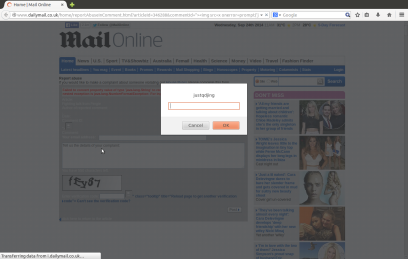
The vulnerability occurs at “&targetUrl” parameter in “logout.html?” page, i.e.
http://www.dailymail.co.uk/registration/logout.html?targetUrl=http%3A%2F%2Fgoogle.com
(2.1) Use the following tests to illustrate the scenario painted above.
The redirected webpage address is “http://diebiyi.com/articles“. Can suppose that this webpage is malicious.
Vulnerable URLs:
http://www.dailymail.co.uk/registration/logout.html?targetUrl=http%3A%2F%2Fdailymail.co.uk
http://www.thisismoney.co.uk/registration/logout.html?targetUrl=http%3A%2F%2Fhao123.com/
http://www.mailonsunday.co.uk/registration/logout.html?targetUrl=http%3A%2F%2Fpinterest.com
POC Code:
http://www.dailymail.co.uk/registration/logout.html?targetUrl=http%3A%2F%2Fdiebiyi.com/articles
http://www.thisismoney.co.uk/registration/logout.html?targetUrl=http%3A%2F%2Fdiebiyi.com/articles
http://www.mailonsunday.co.uk/registration/logout.html?targetUrl=http%3A%2F%2Fdiebiyi.com/articles
POC Video:
https://www.youtube.com/watch?v=AU-HJGe5BWE&feature=youtu.be
Blog Detail:
http://tetraph.com/security/website-test/daily-mail-url-redirection/
http://securityrelated.blogspot.com/2015/10/daily-mail-registration-page.html
https://vulnerabilitypost.wordpress.com/2015/10/30/daily-mail-open-redirect/
(2.2) The program code flaw can be attacked without user login. Tests were performed on Microsoft IE (9 9.0.8112.16421) of Windows 8, Mozilla Firefox (37.0.2) & Google Chromium 42.0.2311 (64-bit) of Ubuntu (14.04.2),and Apple Safari 6.1.6 of Mac OS X v10.9 Mavericks.
These bugs were found by using URFDS (Unvalidated Redirects and Forwards Detection System).
(2) Description of Open Redirect:
Here is the description of Open Redirect: “A web application accepts a user-controlled input that specifies a link to an external site, and uses that link in a Redirect. This simplifies phishing attacks. An http parameter may contain a URL value and could cause the web application to redirect the request to the specified URL. By modifying the URL value to a malicious site, an attacker may successfully launch a phishing scam and steal user credentials. Because the server name in the modified link is identical to the original site, phishing attempts have a more trustworthy appearance.” (From CWE)
(3) Vulnerability Disclosure:
These vulnerabilities have not been patched.
Discover and Reporter:
Wang Jing, Division of Mathematical Sciences (MAS), School of Physical and Mathematical Sciences (SPMS), Nanyang Technological University (NTU), Singapore. (@justqdjing)
http://www.tetraph.com/wangjing
Reference:
https://cxsecurity.com/issue/WLB-2015110028
http://computerobsess.blogspot.com/2015/11/daily-mail-open-redirect.html
http://itinfotech.tumblr.com/post/132726134291/ithut-daily-mail-registration-page-unvalidated
http://itsecurity.lofter.com/post/1cfbf9e7_8d45d37
https://inzeed.wordpress.com/2015/11/07/daily-mail-registration-page
http://webtechhut.blogspot.com/2015/11/daily-mail-registration-page.html
https://community.webroot.com/t5/Security-Industry-News/The-Telegraph-and-Daily-Mail
http://permalink.gmane.org/gmane.comp.security.fulldisclosure/2643|
http://lists.openwall.net/full-disclosure/2015/11/03/8